D2. Not-so-Simple Mail Protocol
Points: 100
Level: Not as Difficult
Category: Log Analysis, Forensic Analysis (E-mail)
Description
A menacing extortion email was received from an unknown sender, claiming that sensitive data has been stolen from the company. The email demands a ransom and threatens to release the data if the demand is not met within 48 hours. It’s clear based on the [extortion email] that the sender attempted to send this email before since the demand’s due date is relative. Find the first email sent so we can estimate a lower bound on the deadline for the legal and finance teams to plan around.
Objective
Use the log dashboard server, Insightful Horizon (https://target-osd.chals.io/) to find the first extortion email from this incident. Username: analyst | Password: ***.
Use the email address that sent the email as the flag. If the server is not loading there are two additional servers that host the exact same data:
- https://target-osd-2.chals.io
- https://target-osd-3.chals.io
Flag Format
An email address, for example: example@wicys.example. The flag IS NOT case-sensitive.
Tools Used
Web Browser, OpenSearch Dashboards
Methodology
The objectives provided the credentials to log into Insightful Horizon.
From challenge D1, the sender’s information was noted: date, time, and to whom it was sent as March 22, 2025; 252.44.98.29; 9:10 PM; security@personalyz.io. A query was performed on Insightful Horizon based on the sender’s IP address (252.44.98.29) to locate the email logs.
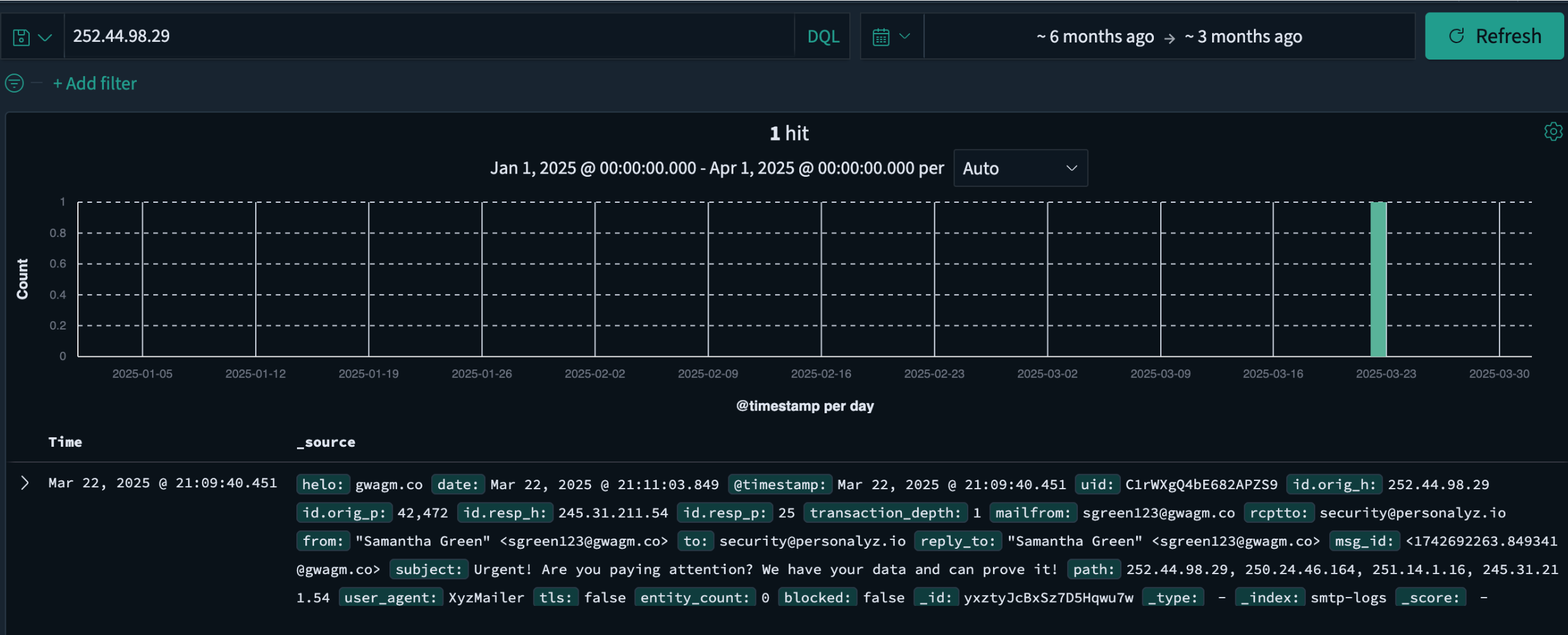
Additional filters were applied based on the results of this search, such as security@personalyz.io and data that would reference potential data theft.
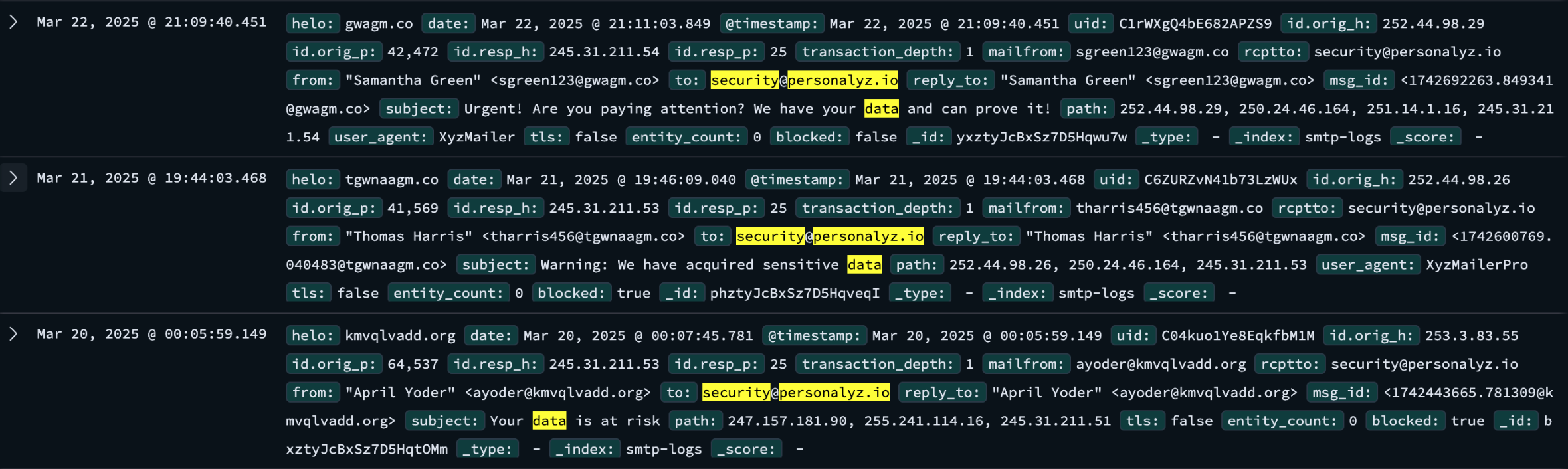
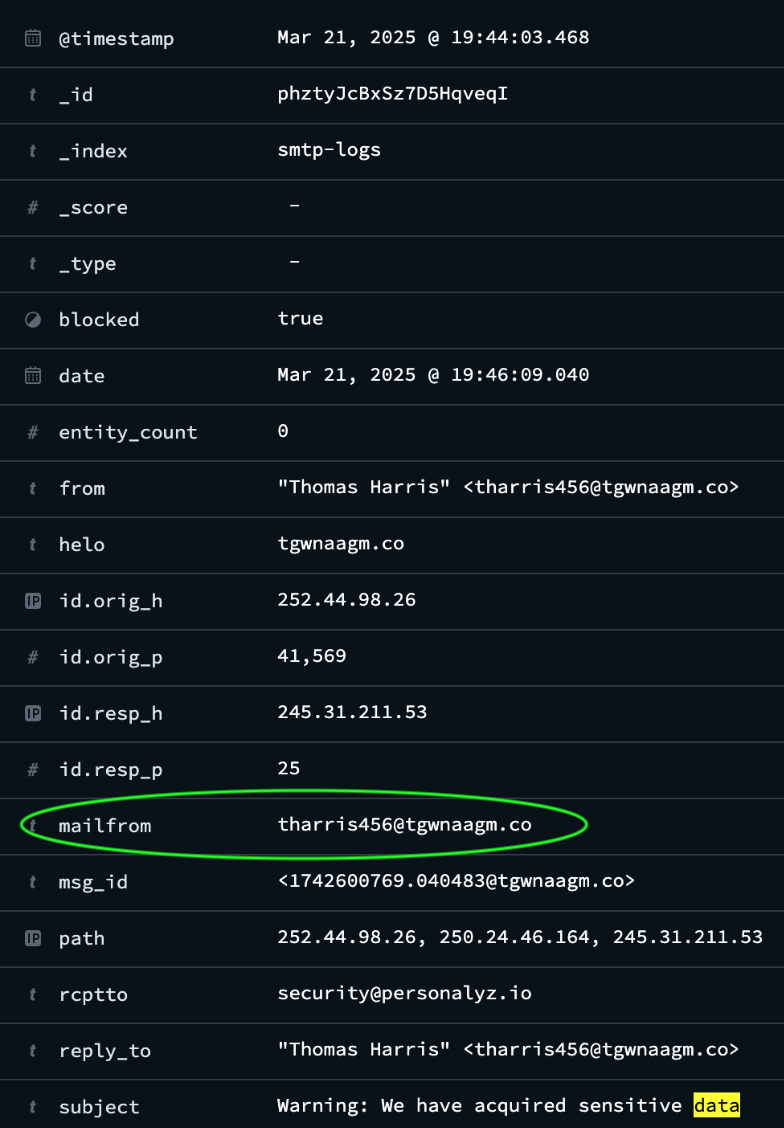
I reviewed the data and noticed that one entry dated, March 21, 2025, included the following subject line, “Warning: We have acquired sensitive data,” which sounded similar to the extortion email from D1. Therefore, this entry log was the first extortion email sent by the threat actor. I found two ways to obtain the sender’s email address. Either reading directly inside the log entry or by expanding the log:
Flag
tharris456@tgwnaagm.co
MITRE ATT&CK
(Suggested)
- Phishing (T1566): Under Initial Access this technique aligns in this challenge, since the threat actor attempted to deliver a malicious message to pressure the target.
- Indicator Removal on Host (T1070): It’s relevant because analyzing the log required understanding potential obfuscation or hiding of sender information within email records.
- Exfiltration Over Alternative Protocol (T1048): It applies indirectly, as the extortion email represents the adversary’s attempt to extract value by coercing the organization based on stolen or sensitive data.